Financial apps handle money, identity documents, and regulated transactions. Every link a user taps carries different stakes than it would in a food delivery app or a social network. A broken deep link in a banking app does not just create a bad experience; it can block a wire transfer, stall a loan application, or trigger a fraud alert that locks someone out of their account.
Deep linking fintech apps means solving two problems at once: getting users to the right screen quickly and doing it without exposing sensitive financial data in transit. This article covers the specific patterns, security requirements, and compliance constraints that make deep linking in financial applications different from other mobile categories.
 Photo by Ivan Samkov on Pexels
Photo by Ivan Samkov on Pexels
Why Fintech Deep Linking Is Different
Most deep linking guides assume you are linking to a product page, a social profile, or a piece of content. Fintech deep links point to things like pending wire transfers, account statements, KYC verification steps, and fraud dispute forms. The differences show up in three areas.
Compliance requirements sit between you and the user. Regulations like PCI DSS, SOC 2, and GDPR constrain what data you can include in a URL, how long a link should remain valid, and what you must log (or not log) about link clicks. A deep link that passes a full account number as a query parameter would violate PCI DSS requirements for protecting cardholder data.
Authentication is non-negotiable. Unlike an e-commerce app that might let unauthenticated users browse products, a banking app must verify identity before showing any account data. Every deep link lands on a gate: biometric prompt, PIN entry, or a full login screen. The challenge is preserving the user's intended destination through that authentication flow so they do not end up on a generic home screen after logging in.
The cost of errors is higher. A deep link to a payment confirmation screen that shows the wrong amount, or a link that reaches the wrong user because of a caching mistake, creates real financial liability. Fintech teams need tighter controls on link generation, validation, and expiration than most other app categories.
Common Fintech Deep Link Patterns
Financial apps use deep links across dozens of user journeys. Here are the patterns that come up most often.
Payment requests. A user sends a payment request to a friend. The link opens the app directly to a pre-filled payment screen with the amount, recipient, and an optional note. If the recipient does not have the app installed, the link falls back to a web checkout or an app store page.
Account alerts. Low balance warnings, large transaction notifications, and deposit confirmations all link to specific transaction detail screens or account overview pages.
Document signing. Loan agreements, account opening disclosures, and regulatory consent forms often require electronic signatures. Deep links take users straight to the document within the app rather than opening a separate e-signature service.
KYC verification flows. "Complete your identity verification" links drop users into the exact step they left off: upload a photo ID, take a selfie, or confirm their address. Our guide on KYC flow deep links covers these patterns in detail.
Statement delivery. Monthly statements and tax documents (1099s, annual summaries) link directly to the document viewer inside the app.
Fraud dispute flows. "Was this you?" links from fraud detection systems need to open directly to a transaction review screen where the user can confirm or deny the charge.
Each of these patterns has its own security and UX constraints, but they all share one requirement: the deep link must survive the authentication step without losing context.
Security Considerations
Financial deep links must follow a strict set of rules that other app categories can often ignore. For a comprehensive treatment of this topic, see fintech deep link security.
Never Put Sensitive Data in URLs
This is the most important rule. URLs get logged in server access logs, browser history, analytics platforms, CDN edge logs, and proxy servers. A deep link like this is a security incident waiting to happen:
# NEVER do this
https://app.example.com/transfer?account=4532015112830366&amount=500&routing=021000021
Instead, use opaque tokens that resolve to the actual data server-side:
# Do this instead
https://app.example.com/transfer?ref=txn_a8f3k29x
The token txn_a8f3k29x maps to the transaction details in your backend. The URL itself reveals nothing about the user's financial data. If the link is intercepted, shared accidentally, or logged by an intermediary, no sensitive information is exposed.
Use HTTPS Exclusively
This should go without saying, but every deep link in a financial app must use HTTPS. HTTP links are vulnerable to man-in-the-middle attacks, and both Apple's Universal Links and Android App Links require HTTPS for the associated domain verification files (apple-app-site-association and assetlinks.json).
Expire Links Aggressively
A payment request link that is still valid six months later is a risk. Someone could forward it, and the recipient might unknowingly authorize a stale payment. Financial deep links should have short expiration windows.
For example, payment request links might expire after 24 hours. Document signing links might be valid for 7 days. Fraud alert links ("Was this you?") should expire within 1 to 2 hours. Route expiration is critical infrastructure for fintech deep linking, not just a nice-to-have.
Validate on the Server, Not Just the Client
When a user taps a deep link and the app opens, the app should call your backend to validate the link token before showing any content. Check that the token exists, has not expired, belongs to the authenticated user, and that the underlying action is still valid (the payment has not already been completed, the document has not already been signed).
// Server-side link validation endpoint
app.get('/api/v1/deep-link/validate', authenticate, async (req, res) => {
const { ref } = req.query;
const linkData = await db.deepLinks.findByToken(ref);
if (!linkData) {
return res.status(404).json({ error: 'Link not found' });
}
if (linkData.expiresAt < new Date()) {
return res.status(410).json({ error: 'Link expired' });
}
if (linkData.userId !== req.user.id) {
// Log this as a potential security event
logger.warn('Deep link accessed by wrong user', {
linkToken: ref,
linkOwner: linkData.userId,
accessedBy: req.user.id
});
return res.status(403).json({ error: 'Unauthorized' });
}
if (linkData.status === 'completed') {
return res.status(409).json({
error: 'Action already completed',
completedAt: linkData.completedAt
});
}
return res.json({
type: linkData.type,
destination: linkData.destination,
metadata: linkData.sanitizedMetadata
});
});
Authentication and Deep Links
The hardest UX problem in fintech deep linking is the authentication handoff. The user taps a link, the app opens, and they need to log in before they can see anything. If you do not handle this carefully, the user logs in and lands on the home screen with no memory of why they opened the app.
Preserving Intent Through Authentication
The standard approach is to store the deep link destination before presenting the login screen, then redirect after successful authentication.
On iOS with Swift:
class DeepLinkHandler {
private var pendingDeepLink: URL?
func handleIncomingLink(_ url: URL) {
if AuthManager.shared.isAuthenticated {
navigateToDestination(url)
} else {
// Store the link and present login
pendingDeepLink = url
presentLoginScreen()
}
}
func onAuthenticationSuccess() {
if let pending = pendingDeepLink {
pendingDeepLink = nil
navigateToDestination(pending)
}
}
private func navigateToDestination(_ url: URL) {
guard let components = URLComponents(url: url, resolvingAgainstBaseURL: true),
let ref = components.queryItems?.first(where: { $0.name == "ref" })?.value else {
return
}
// Validate the link server-side before navigating
APIClient.validateDeepLink(token: ref) { result in
switch result {
case .success(let linkData):
Router.navigate(to: linkData.destination)
case .failure(let error):
self.showLinkError(error)
}
}
}
}
On Android with Kotlin:
class DeepLinkActivity : AppCompatActivity() {
override fun onCreate(savedInstanceState: Bundle?) {
super.onCreate(savedInstanceState)
val deepLinkUri = intent.data ?: return
if (AuthManager.isAuthenticated) {
resolveAndNavigate(deepLinkUri)
} else {
// Store deep link in encrypted shared preferences
DeepLinkStore.savePendingLink(this, deepLinkUri.toString())
startActivity(Intent(this, LoginActivity::class.java))
finish()
}
}
private fun resolveAndNavigate(uri: Uri) {
val ref = uri.getQueryParameter("ref") ?: return
lifecycleScope.launch {
try {
val linkData = apiClient.validateDeepLink(ref)
Navigator.navigateTo(linkData.destination)
} catch (e: LinkExpiredException) {
showExpiredLinkDialog()
} catch (e: UnauthorizedException) {
showUnauthorizedDialog()
}
}
}
}
Biometric Gates
Many banking apps require biometric authentication (Face ID, Touch ID, fingerprint) even for already-authenticated users when accessing sensitive screens. Deep links that lead to transaction details, payment confirmations, or account settings should trigger a biometric prompt before showing content.
The key is to make the biometric check part of the navigation flow, not a separate step the user has to figure out. Tap the link, see the biometric prompt, see the content. Three steps, no confusion.
Session Timeout Handling
Financial apps typically enforce aggressive session timeouts (5 to 15 minutes of inactivity). A user who taps a deep link after their session has expired should see a login screen, not an error. After re-authenticating, they should arrive at the deep link's destination, not the home screen.
Store the pending deep link destination in encrypted local storage (Keychain on iOS, EncryptedSharedPreferences on Android) so it survives the re-authentication flow.
Compliance Requirements
Deep linking in financial apps intersects with several compliance frameworks. Here is what matters for each.
PCI DSS
The Payment Card Industry Data Security Standard prohibits storing or transmitting cardholder data (card numbers, CVVs, expiration dates) in plaintext. Deep link URLs must never contain this data. Use opaque reference tokens instead.
PCI DSS also requires logging access to cardholder data. If a deep link leads to a screen that displays card information, log that the link was used, by whom, and when. Your webhook integration can feed these events into your compliance logging pipeline.
SOC 2
SOC 2 audits look at access controls, system monitoring, and data protection. For deep linking, this means:
- Links must be scoped to the correct user (no cross-user access via link manipulation).
- Link creation, usage, and expiration events should be logged.
- Failed deep link validation attempts (expired, wrong user, tampered tokens) should trigger monitoring alerts.
GDPR
The General Data Protection Regulation affects deep link analytics. If you are tracking deep link clicks with IP addresses, device fingerprints, or user identifiers, that data is personal data under GDPR. You need a lawful basis for processing it, and you must honor deletion requests.
This is relevant for analytics and attribution. When you track which deep links users click, how often, and from which channels, you are collecting personal data. Your deep link analytics platform needs to support data deletion requests and provide data processing agreements.
Tolinku's analytics and attribution features are designed with privacy controls that help fintech teams meet these requirements without sacrificing visibility into link performance.
Payment Links and Money Transfer Deep Links
Payment links are the most common deep link type in fintech apps. Whether it is a peer-to-peer payment request, a merchant checkout link, or an invoice payment, the pattern is similar.
Generating Payment Deep Links
The backend generates a payment link with an opaque token. The token maps to the payment details stored securely on the server.
interface PaymentLinkData {
amount: number;
currency: string;
recipientId: string;
note?: string;
expiresAt: Date;
}
async function createPaymentLink(data: PaymentLinkData): Promise<string> {
const token = crypto.randomBytes(16).toString('hex');
await db.paymentLinks.create({
token,
amount: data.amount,
currency: data.currency,
recipientId: data.recipientId,
note: data.note,
expiresAt: data.expiresAt,
status: 'pending',
createdAt: new Date()
});
// The deep link URL contains only the token
return `https://pay.yourbank.com/r/${token}`;
}
Handling Payment Confirmation
When the user taps the link and authenticates, the app fetches the payment details from the server and presents a confirmation screen. The user reviews the amount, recipient, and note, then confirms with biometric authentication.
Never auto-execute a payment from a deep link. Always require explicit user confirmation. This protects against phishing attacks where someone sends a fraudulent payment link.
Pre-filled Transfer Forms
For money transfer deep links, you can pre-fill the transfer form using dynamic routes. The user taps a link like https://pay.yourbank.com/send/ref_abc123, and the app opens with the recipient and amount pre-filled. The user reviews and confirms. This cuts several steps out of the transfer flow and reduces drop-off rates significantly.
Onboarding Flows for Fintech
Fintech onboarding is one of the highest-friction experiences in mobile apps. Users need to provide personal information, upload identity documents, link bank accounts, and sometimes wait for manual verification. Deep links can reduce friction at several points. For more on onboarding optimization, see banking app onboarding deep links.
Referral Programs
Referral deep links for fintech apps carry referral codes that attribute new users to existing customers. The link needs to survive the app install process (deferred deep linking) so the referral credit applies even when the new user installs the app from the App Store or Google Play before opening the link.
https://links.yourbank.com/refer?code=ALICE2026
When the new user installs and opens the app, the deferred deep link resolves the referral code and pre-fills it during signup. The referrer gets their bonus after the new user completes onboarding. Tolinku's deep linking features handle deferred deep link resolution across both iOS and Android, preserving the referral attribution through the install.
KYC Deep Links
When a user starts the KYC process but drops off (as most do), you can send follow-up emails or push notifications with deep links that return them to the exact step they abandoned.
"Upload your photo ID" links to the document capture screen. "Verify your address" links to the address confirmation step. "Review your application" links to a summary page. Each link includes a token that maps to the user's KYC session, so the app knows exactly where they left off.
Account Funding
After a user creates an account, the first deposit is a critical activation metric. Deep links in "Fund your account" emails or push notifications can open directly to the deposit screen with suggested amounts. Reducing the number of taps between notification and deposit completion measurably improves funding rates.
Push Notification Deep Links
Push notifications are the primary channel for time-sensitive financial communications. Every push notification in a banking app should carry a deep link payload.
Transaction Alerts
{
"title": "Purchase: $47.23 at Whole Foods",
"body": "Tap to view transaction details",
"data": {
"deep_link": "https://links.yourbank.com/txn/ref_9x8f2a",
"type": "transaction_alert",
"priority": "normal"
}
}
When the user taps this notification, the app opens directly to the transaction detail screen for that specific purchase. Without a deep link, the user would land on the home screen and have to navigate to recent transactions manually.
Fraud Alerts
Fraud alert deep links require special handling. They are time-sensitive (the user needs to respond quickly), they must be scoped to the correct user (showing another user's suspicious transaction would be a serious breach), and they should trigger re-authentication before displaying transaction details.
{
"title": "Unusual activity detected",
"body": "We noticed a charge you may not recognize. Tap to review.",
"data": {
"deep_link": "https://links.yourbank.com/fraud/ref_k3m9p1",
"type": "fraud_alert",
"priority": "high",
"requires_biometric": true
}
}
The requires_biometric flag tells the app to present a biometric prompt immediately, even if the user has an active session. This extra verification step protects against scenarios where someone else has access to the device.
Bill Reminders
Bill payment reminder notifications link to the bill payment screen with the biller and amount pre-populated. The user taps the notification, authenticates, reviews the payment details, and confirms. Three steps from notification to paid bill.
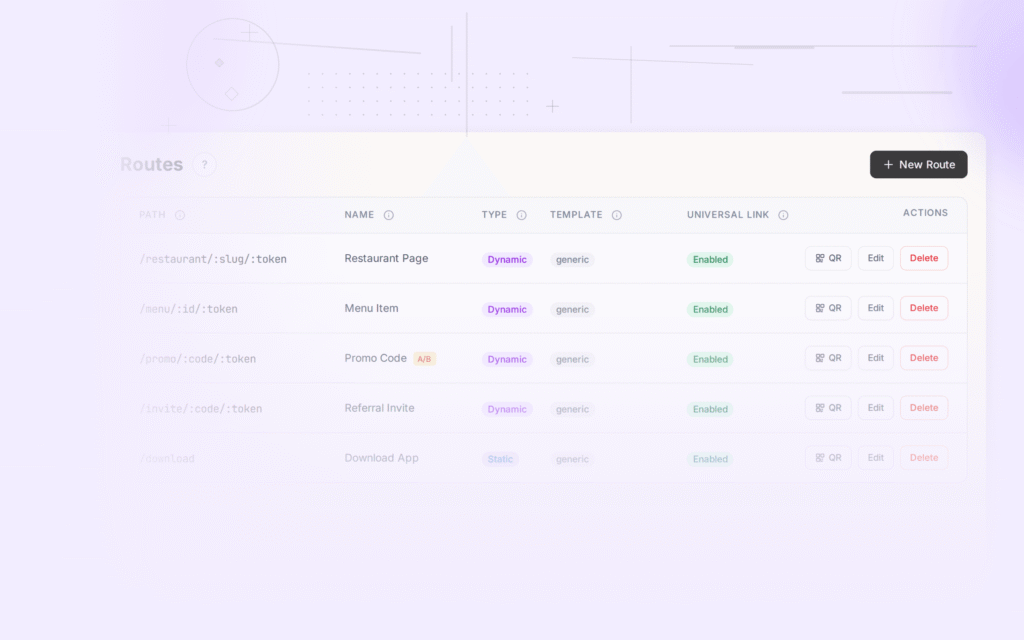
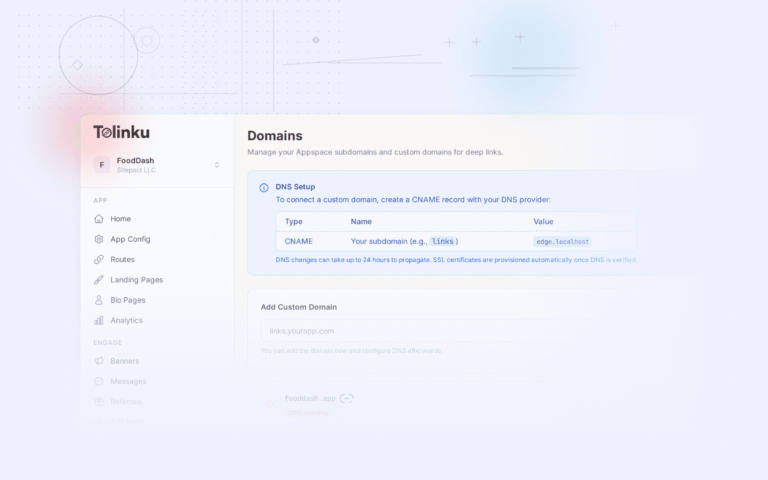
Implementation with Tolinku
Setting up deep linking for a fintech app with Tolinku involves configuring routes that match your app's URL patterns, setting expiration policies, and connecting webhooks for compliance logging.
Route Configuration
Define routes for each deep link pattern in your app. A payment link route might look like this:
Pattern: /pay/:token
iOS Target: yourbank://pay?ref={{token}}
Android Target: yourbank://pay?ref={{token}}
Fallback: https://yourbank.com/pay/{{token}}
The :token parameter in the route captures the opaque reference and passes it through to the app. The fallback URL handles cases where the app is not installed, directing users to a web version of the payment flow or the app store.
Link Expiration
Configure route-level expiration based on the type of financial action. Payment links expire after 24 hours. Fraud alert links expire after 2 hours. Document signing links expire after 7 days. When a link expires, users see a clear message explaining that the link is no longer valid and directing them to open the app directly.
Webhook Integration
Connect webhooks to your compliance logging system. Every deep link click event fires a webhook with the link token, timestamp, and anonymized device information. This data feeds into your SOC 2 audit trail and helps your security team monitor for anomalous link usage patterns (such as a single fraud alert link being clicked hundreds of times, which might indicate a phishing campaign using your link format).
Analytics
Track deep link performance across channels without exposing personal financial data. Measure conversion rates from push notification deep links versus email deep links. Identify which onboarding steps have the highest drop-off rates when accessed via deep link versus in-app navigation. Tolinku's analytics dashboard provides this visibility while keeping user-level data properly scoped.
Best Practices
Here is a summary of the rules that matter most for fintech deep linking.
Use opaque tokens, never raw data. Every deep link URL should contain only a reference token that resolves to the actual data on your server. Account numbers, card numbers, transaction amounts, and personal information must never appear in a URL.
Expire links based on their action type. Not all links need the same lifetime. Payment links: 24 hours. Fraud alerts: 1 to 2 hours. Statements: 30 days. Referral links: 90 days. Set defaults per route and allow overrides when generating individual links.
Always validate server-side. When the app receives a deep link, call your backend to verify the token before showing any content. Check token existence, expiration, user ownership, and action status (has it already been completed?).
Require authentication before showing financial data. Every deep link destination that displays account information, transaction details, or payment forms must sit behind an authentication gate. Store the pending destination and restore it after login.
Add biometric verification for sensitive actions. Payment confirmations, fund transfers, and fraud dispute responses should require biometric authentication even if the user has an active session.
Log everything for compliance. Deep link creation, click, validation, expiration, and completion events all belong in your audit log. Configure webhooks to stream these events to your SIEM or compliance logging platform.
Handle the uninstalled case gracefully. When a user taps a payment link but does not have your app installed, show a web-based version of the payment flow or a clear prompt to install the app. Do not just drop them on a generic app store page with no context.
Test link expiration end-to-end. Expired link behavior is easy to overlook during development. Write tests that create a link, advance the clock past its expiration, and verify that the app shows the correct expired state rather than a generic error.
Do not auto-execute financial actions from deep links. Always show a confirmation screen. A user who taps a payment deep link should see the payment details and explicitly confirm. This protects against phishing and accidental clicks.
Use HTTPS for everything. Deep link domains, associated domain verification files, API endpoints, and webhook callbacks should all use TLS. HTTP has no place in a financial application's link infrastructure.
Conclusion
Deep linking in fintech and banking apps follows the same fundamental principles as any other app category: get users to the right screen as fast as possible. But the constraints are tighter. You cannot put sensitive data in URLs. You must authenticate before showing content. You need to expire links aggressively. And you have to log every interaction for compliance audits.
The good news is that these constraints, once implemented, make your deep linking infrastructure more reliable for everyone. Opaque tokens are more maintainable than URLs packed with query parameters. Server-side validation catches bugs that client-side routing would miss. Expiration policies prevent stale links from causing confusion months later.
Start with the highest-impact deep link patterns (payment requests, fraud alerts, and onboarding flows), get the authentication handoff right, and build from there. The technical foundation you set up for fintech deep linking will serve you well as your app grows and your link volume increases.
Get deep linking tips in your inbox
One email per week. No spam.